Finance
What Is Credit Card Tokenization
Published: November 9, 2023
Learn how credit card tokenization works and why it's important in the finance industry. Discover how this technology helps secure sensitive financial information.
(Many of the links in this article redirect to a specific reviewed product. Your purchase of these products through affiliate links helps to generate commission for LiveWell, at no extra cost. Learn more)
Table of Contents
- Introduction
- Definition of Credit Card Tokenization
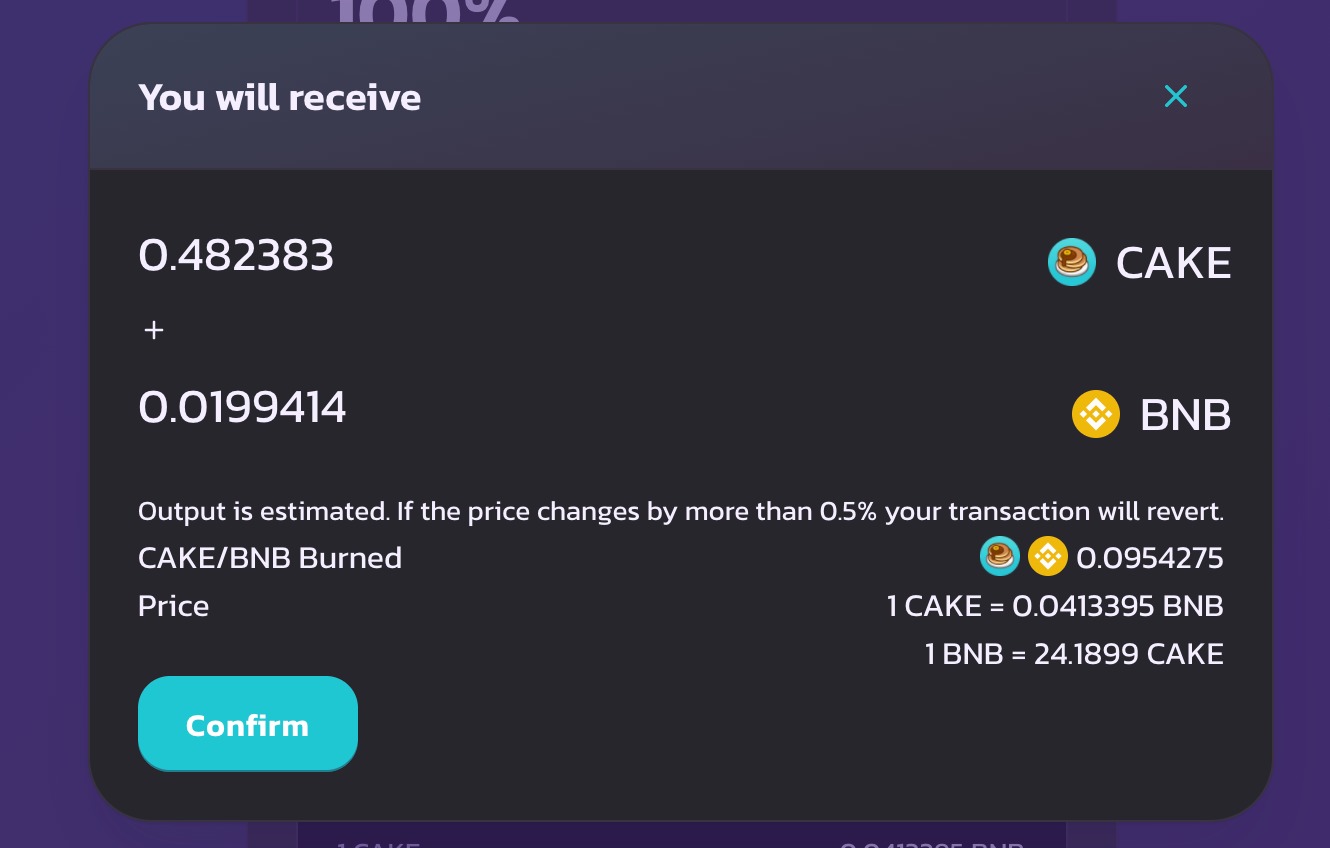
- How Credit Card Tokenization Works
- Benefits of Credit Card Tokenization
- Challenges of Credit Card Tokenization
- Implementing Credit Card Tokenization
- Security Considerations of Credit Card Tokenization
- Comparison with Other Payment Security Technologies
- Future Trends in Credit Card Tokenization
- Conclusion
Introduction
Welcome to the world of credit card tokenization. In today’s digital era, where online transactions are the norm, protecting sensitive financial information has become a top priority. Credit card tokenization is a cutting-edge technology that is revolutionizing the way we secure payment data.
But what exactly is credit card tokenization? How does it work? And what are the benefits and challenges associated with this technology? In this article, we will delve into these questions and explore the implementation, security considerations, and future trends of credit card tokenization.
Credit card tokenization is a method of safeguarding credit card information by replacing the card’s primary account number (PAN) with a unique identifier, known as a token. This token acts as a surrogate for the actual card data, ensuring that sensitive information is shielded from potential data breaches and fraud.
As consumers increasingly embrace online shopping, the risk of credit card theft and fraudulent transactions has grown exponentially. Traditional methods of securing payment data, such as encryption, have limitations. Encryption can be decrypted, exposing the underlying credit card information. This is where credit card tokenization steps in to provide a more robust and secure solution.
With credit card tokenization, the sensitive card data is securely stored in a tokenization system, usually hosted by a trusted third-party provider or a merchant’s own data center. When a transaction is initiated, instead of transmitting the actual credit card details, the token is transmitted through the payment gateway. This process eliminates the need for merchants to store sensitive card information, reducing the risk of data breaches.
Tokenization offers various benefits for both merchants and cardholders. For merchants, it reduces the scope of PCI DSS (Payment Card Industry Data Security Standard) compliance by removing the need to store actual card information. Compliance with these regulations can be time-consuming and costly for businesses, but tokenization simplifies the process. Additionally, tokenization can enhance transaction speeds, since there is no longer a need to decrypt and process large amounts of card data.
For cardholders, tokenization provides peace of mind. With their card information replaced by a unique token, they can shop online with confidence, knowing that their sensitive data is protected. Even if a token is compromised, it cannot be reversed to reveal the actual credit card details, rendering it useless for fraudsters.
While credit card tokenization offers numerous advantages, it does come with its own set of challenges. Implementation can be complex, requiring integration with existing payment systems and the adoption of tokenization standards. Additionally, some industries, such as healthcare or finance, may face regulatory hurdles when implementing tokenization.
Now that we have introduced credit card tokenization and its benefits and challenges, in the following sections, we will explore how tokenization works, security considerations, comparisons with other payment security technologies, and the future trends of this revolutionary technology.
Definition of Credit Card Tokenization
Credit card tokenization is a data security technique that is designed to protect sensitive credit card information during online transactions. It involves replacing the actual credit card number with a unique identifier called a token. This token serves as a surrogate for the card information, allowing for secure and seamless payment processing.
The tokenization process begins when a customer enters their credit card details on a website or mobile app to make a purchase. Instead of directly transmitting the sensitive card information to the merchant or payment processor, it is encrypted and securely stored in a tokenization system. This system can be either hosted by a trusted third-party service provider or maintained by the merchant themselves. The tokenization system assigns a unique token to the credit card data and stores the tokenized information in its database.
The generated token is then returned to the merchant or payment processor, who can use it for subsequent transactions without having to store or transmit the actual credit card number. This means that the merchant’s systems are never exposed to the sensitive card data, minimizing the risk of data breaches and reducing the scope of regulatory compliance requirements.
It is important to note that credit card tokenization is not the same as encryption. While encryption converts data into an unreadable format and requires a decryption key to convert it back, tokenization replaces the original data with a surrogate value that has no mathematical relationship to the original card data. Tokens cannot be mathematically reversed or decrypted to obtain the credit card number, providing an added layer of security.
Tokenization can be implemented at various stages of the payment processing ecosystem, including at the point of sale (POS), online payment gateways, and within payment service providers. Tokens can also be specific to a particular merchant, making them useless if intercepted during transmission or in the event of a data breach.
It is worth mentioning that credit card tokenization is not limited to just credit card information. It can also be applied to other sensitive data such as bank account numbers, social security numbers, or any other type of personally identifiable information (PII) that needs to be protected.
In summary, credit card tokenization is a secure method of protecting credit card data during online transactions. By replacing the actual credit card number with a token, merchants and payment processors can reduce the risk of data breaches, enhance customer trust, and streamline payment processing.
How Credit Card Tokenization Works
Credit card tokenization works by replacing the sensitive credit card information with a unique token, which acts as a surrogate for the actual card data. This process involves several steps to ensure the security and integrity of the payment data.
1. Data Collection: When a customer enters their credit card details during an online transaction, the payment application captures the information, including the credit card number, expiration date, and CVV code.
2. Encryption: The collected credit card data is encrypted using strong cryptographic algorithms. This encryption process converts the card information into an unreadable format, rendering it useless if intercepted during transmission or storage.
3. Token Generation: In the tokenization process, a unique token is generated to replace the actual credit card number. This token is typically a random string of characters and is associated with the encrypted card data in the tokenization system’s database.
4. Storage: The encrypted credit card data is securely stored in the tokenization system, either within a merchant’s own data center or with a trusted third-party service provider. It is important to note that the tokenization system does not store the actual credit card information, only the encrypted version.
5. Return Token: The generated token is returned to the merchant’s payment application or the payment gateway. This token is used to identify the customer’s credit card data for future transactions without exposing the sensitive information.
6. Transaction Processing: When a customer initiates a subsequent transaction, the payment application or gateway sends the token to the tokenization system to retrieve the associated encrypted credit card data. The system decrypts the information using the appropriate decryption key, allowing the transaction to be processed.
It is important to note that the tokenization process is transparent to both the merchant and the customer. From the merchant’s perspective, the token functions like a credit card number and can be used for payment processing in the same way. And from the customer’s perspective, the token allows for seamless and secure transactions without the need to repeatedly provide their credit card details.
Credit card tokenization offers several advantages over traditional payment security methods. First and foremost, it significantly reduces the risk of data breaches since the actual credit card information is never stored or transmitted. It also helps businesses achieve and maintain compliance with industry regulations, such as the Payment Card Industry Data Security Standard (PCI DSS).
In summary, credit card tokenization works by replacing sensitive credit card information with a unique token. This process ensures the security of the payment data and provides convenience for both merchants and customers during online transactions.
Benefits of Credit Card Tokenization
Credit card tokenization offers a wide range of benefits for both merchants and customers. This innovative technology enhances payment security, simplifies compliance requirements, and improves the overall transaction experience. Let’s explore the key advantages of credit card tokenization:
1. Enhanced Security: Credit card tokenization provides an added layer of security by removing the need to store or transmit actual credit card numbers. Tokens have no mathematical relationship to the original card data, making them useless for fraudsters even if intercepted. This significantly reduces the risk of data breaches and protects customers’ sensitive financial information.
2. Simplified Compliance: Credit card tokenization helps merchants simplify their compliance with industry regulations. By reducing the storage and transmission of actual credit card information, the scope of the Payment Card Industry Data Security Standard (PCI DSS) requirements is significantly reduced. This saves time, effort, and resources that would have been otherwise spent on ensuring compliance.
3. Faster Payment Processing: Tokenization can improve transaction speeds by eliminating the need to decrypt and process large amounts of credit card data. With tokens in place, payment processing systems can quickly retrieve the necessary information to complete a transaction, resulting in faster, more efficient transactions.
4. Increased Customer Trust: Credit card tokenization helps build trust with customers by ensuring the security of their payment information. With sensitive credit card details replaced by tokens, customers can feel confident that their data is protected, reducing anxieties about potential fraud or identity theft.
5. Seamless User Experience: Through tokenization, customers enjoy a seamless transaction experience. They can make subsequent purchases without needing to repeatedly enter their credit card details, improving convenience and reducing friction in the checkout process. This can lead to higher customer satisfaction and increased loyalty.
6. Versatility: Credit card tokenization is applicable to various payment methods, including traditional cards, mobile wallets, and other emerging payment technologies. This versatility allows businesses to adapt and incorporate new payment methods without compromising security.
7. Reducing Data Storage Costs: Since tokenization removes the need to store sensitive credit card information, businesses can significantly reduce the costs associated with data storage and security. This includes investments in secure data centers, encryption technologies, and ongoing monitoring and maintenance.
8. Mitigating Fraud Risks: Tokenization mitigates the risk of fraudulent transactions by rendering stolen tokens useless without access to the original credit card data. Even if a token is compromised, it cannot be reversed to expose the actual card details, providing an additional layer of protection against fraud.
In summary, credit card tokenization offers numerous benefits, including enhanced security, simplified compliance, faster payment processing, increased customer trust, seamless user experience, and cost reductions. By leveraging tokenization, businesses can protect their customers’ financial information and provide a secure and convenient payment environment.
Challenges of Credit Card Tokenization
While credit card tokenization offers significant advantages in terms of payment security and compliance, there are several challenges that businesses may encounter when implementing this technology. It’s important to be aware of these challenges in order to effectively navigate the tokenization process. Some of the key challenges of credit card tokenization are:
1. Implementation Complexity: Implementing credit card tokenization can be a complex process, especially for businesses with existing payment systems that need to be integrated. It requires coordination between the tokenization system provider, payment processors, and other stakeholders to ensure a seamless implementation. This can involve additional customization and development work, potentially increasing costs and deployment timelines.
2. Adoption of Token Standards: Ensuring compatibility and interoperability between different tokenization systems and payment providers can be challenging. The industry is working towards establishing tokenization standards, such as the EMVCo Payment Tokenization Specification, to facilitate consistent tokenization practices. However, until widespread adoption of these standards is achieved, businesses may face complexities in integrating different tokenization systems and payment platforms.
3. Regulatory Considerations: Certain industries, such as healthcare or finance, may have specific regulatory requirements that need to be considered when implementing credit card tokenization. These industries may have additional compliance obligations beyond standard PCI DSS requirements, such as HIPAA (Health Insurance Portability and Accountability Act) or GLBA (Gramm-Leach-Bliley Act). Ensuring compliance with these regulations while implementing tokenization can be a challenge that requires careful planning and coordination.
4. Legacy Systems Integration: For businesses with legacy payment systems, integrating credit card tokenization can be challenging. These systems may not have built-in support for tokenization, requiring additional development or the use of intermediary services. The process of retrofitting legacy systems to work with tokenization can be complex and may require significant technical expertise.
5. Tokenization Storage and Retrieval: Businesses must ensure that the tokenization system used can efficiently store and retrieve tokenized data. Organizations with high transaction volumes need to consider the scalability and performance of the system to handle the increased load. Additionally, efficient token lookup and retrieval mechanisms need to be in place to support seamless transaction processing in real-time.
6. Changing Tokenization Providers: If a business decides to switch tokenization providers, challenges can arise in transitioning from one system to another. Migration of existing tokens and ensuring compatibility between different tokenization platforms may require careful planning and coordination to avoid service interruptions or data loss.
7. Education and Training: Employees and stakeholders involved in the tokenization process need to be educated and trained on the technology and its implementation. This includes understanding tokenization concepts, ensuring data privacy and security, and adhering to token usage protocols. Proper training is essential to maintain the integrity and security of the tokenized payment data.
Despite these challenges, credit card tokenization offers significant advantages in terms of data security and compliance. By carefully addressing these challenges and collaborating with experienced vendors and technology partners, businesses can successfully implement and leverage the benefits of credit card tokenization.
Implementing Credit Card Tokenization
Implementing credit card tokenization involves careful planning, coordination, and collaboration between various stakeholders. The process requires consideration of technical integration, compliance requirements, and selecting the right tokenization solution provider. Here are the key steps involved in implementing credit card tokenization:
1. Assess Current Payment Infrastructure: Start by assessing your current payment infrastructure to identify potential points of vulnerability and areas for improvement. Evaluate your existing payment systems, including point-of-sale (POS) terminals, e-commerce platforms, and payment gateways, to determine compatibility with tokenization.
2. Define Tokenization Strategy: Define your tokenization strategy based on your specific business needs and goals. Determine what types of data will be tokenized, such as credit card numbers, expiration dates, and CVV codes. Consider whether tokenization will be performed in-house or through a trusted third-party service provider.
3. Select a Tokenization Solution Provider: Evaluate and select a reputable tokenization solution provider that meets your specific requirements. Consider factors such as security, scalability, compliance, integration capabilities, and customer support. Ensure the provider has a track record of successfully implementing tokenization and a solid reputation in the industry.
4. Integration and Testing: Work closely with your tokenization solution provider to integrate the tokenization system into your existing payment infrastructure. This may involve working with your payment gateway provider or processor to enable the tokenization process. Conduct thorough testing to ensure the seamless transfer and retrieval of tokens during transactions.
5. Compliance Considerations: Ensure compliance with industry regulations, such as the Payment Card Industry Data Security Standard (PCI DSS), when implementing tokenization. Understand the impact of tokenization on your compliance obligations and ensure that the tokenization solution provider is compliant with the necessary industry standards and certifications.
6. Employee Education and Training: Educate and train your employees on the proper handling of tokenized data and the new payment processes. Ensure that they understand the importance of data privacy and security, as well as any specific protocols associated with token usage. Provide ongoing training to keep employees up to date with best practices and emerging security trends.
7. Monitor and Update: Regularly monitor the tokenization system and its performance to identify any potential issues or vulnerabilities. Stay updated with new developments in tokenization technology and ensure that your systems are up to date with the latest security patches and enhancements. Periodically review your tokenization strategy to ensure that it aligns with your evolving business needs and compliance requirements.
Implementing credit card tokenization requires a well-planned and coordinated effort. By following these steps and working closely with your tokenization solution provider, you can successfully integrate tokenization into your existing payment infrastructure, enhance data security, and provide a secure payment environment for your customers.
Security Considerations of Credit Card Tokenization
Credit card tokenization is widely recognized as a highly secure method for protecting sensitive payment data. However, like any security measure, it is important to be aware of potential vulnerabilities and take necessary precautions to ensure the highest level of protection. Here are key security considerations to keep in mind when implementing credit card tokenization:
Data Encryption: Ensure that the credit card data is properly encrypted before it is sent to the tokenization system. Encryption converts the sensitive information into an unreadable format, providing an additional layer of security. Make sure that strong cryptographic algorithms and key management practices are in place to safeguard the encryption process.
Tokenization System Security: Choose a tokenization solution provider that adheres to strict security protocols. The tokenization system should have robust security measures in place, such as encryption of stored data, secure authentication mechanisms, and regular security audits. Implement stringent access controls to restrict unauthorized access to the tokenization system and closely monitor system activity for any suspicious behavior.
Secure Token Transmission: Implement secure transmission protocols, such as Transport Layer Security (TLS) or Secure Sockets Layer (SSL), when transmitting tokens between systems or across networks. These protocols ensure encrypted and secure communication, protecting the integrity and confidentiality of the tokenized data as it travels between different entities.
Secure Storage of Tokens: Pay attention to the secure storage and management of tokens. Ensure that the tokenization system’s database is adequately protected against unauthorized access. Implement strict access controls, data backup procedures, and regularly test the system’s ability to recover in case of data loss or system failure. Follow industry best practices for secure data storage, such as encryption of token storage media and secure key management.
System Monitoring and Intrusion Detection: Employ robust monitoring and intrusion detection systems to detect and respond to any unauthorized attempts or suspicious activities. Implement real-time monitoring of system logs, network traffic, and user activity to quickly identify and mitigate potential security threats or breaches. Regularly review and analyze logs to detect any unusual patterns or signs of unauthorized access or data exfiltration.
Token Revocation and Lifecycle Management: Establish processes and procedures for token lifecycle management. This includes mechanisms for token revocation, such as when a customer’s card is lost or stolen, or if they request to terminate their relationship with your business. Implement a mechanism to ensure that revoked tokens are securely deleted from the tokenization system to prevent any unauthorized usage.
Compliance with Regulatory Standards: Ensure that your credit card tokenization implementation complies with industry regulations, such as the Payment Card Industry Data Security Standard (PCI DSS). Adhere to the required controls, undergo regular audits, and maintain appropriate documentation to demonstrate compliance. Stay updated with changes in the regulatory landscape and ensure that your tokenization practices align with any updated requirements.
Employee Training and Awareness: Educate and train employees involved in tokenization processes about their roles and responsibilities in maintaining the security of tokenized data. Foster a culture of security awareness and emphasize the importance of following proper security protocols, including password management, social engineering prevention, and data handling procedures. Regularly update employees on emerging security threats and best practices.
By considering these security factors and implementing appropriate measures, businesses can ensure the integrity and confidentiality of tokenized credit card data. Credit card tokenization, when implemented correctly, provides a robust security mechanism that protects sensitive payment information and minimizes the risk of data breaches and fraudulent activities.
Comparison with Other Payment Security Technologies
Credit card tokenization is just one of several payment security technologies available to businesses. Let’s compare credit card tokenization with other commonly used payment security technologies to understand their similarities, differences, and respective advantages:
Encryption: Both credit card tokenization and encryption aim to protect sensitive payment data. Encryption transforms the data into an unreadable format using cryptographic algorithms. However, there is a key difference between the two. Encryption requires decryption to retrieve the original data, whereas tokenization replaces the data with a surrogate value (the token). Tokenization offers an additional layer of security, as tokens cannot be mathematically reversed to reveal the original data.
EMV (Europay, Mastercard, and Visa) Chip Technology: EMV chip technology replaces traditional magnetic stripe cards with embedded microchips that generate unique transaction data for every purchase. This technology has been successful in reducing card-present counterfeit fraud. While tokenization primarily focuses on securing card-not-present transactions (e.g., online purchases), EMV chip technology primarily addresses card-present transactions. Combining tokenization and EMV chip technology provides a comprehensive security approach for both online and offline transactions.
3D Secure: 3D Secure is an additional layer of security for online transactions, often referred to as “Verified by Visa,” “Mastercard SecureCode,” or “American Express SafeKey.” It adds an authentication step to the checkout process, requiring users to provide an additional password or unique code to verify their identity. Tokenization and 3D Secure can be complementary technologies, as tokenization protects the payment data, while 3D Secure focuses on authenticating the user.
Biometric Authentication: Biometric authentication utilizes unique physical or behavioral characteristics, such as fingerprints or facial recognition, to verify a user’s identity. While tokenization primarily focuses on securing payment data, biometric authentication adds an additional layer of user identity verification. Incorporating biometric authentication into payment systems, along with tokenization, can enhance security and streamline the user experience.
Point-to-Point Encryption (P2PE): P2PE encrypts payment data at the point of entry (e.g., the payment terminal) and maintains that encryption until it reaches the processor or acquiring bank. Similar to encryption, P2PE protects data in transit. However, unlike tokenization, it does not replace the actual payment data with a surrogate value. P2PE and tokenization can be implemented together to provide end-to-end encryption and tokenization, adding an extra layer of security for payment transactions.
Out-of-Band Authentication: Out-of-Band authentication utilizes channels separate from the primary transaction channel (e.g., SMS, email, or phone call) to verify the user’s identity. It adds an extra level of security by performing the authentication process through a separate communication or channel, reducing the risk of interception or tampering. Tokenization and out-of-band authentication can be combined to ensure secure payment transactions with an added layer of user identity verification.
In summary, credit card tokenization, encryption, EMV chip technology, 3D Secure, biometric authentication, point-to-point encryption, and out-of-band authentication are all valuable payment security technologies with their respective strengths and applications. Combining multiple technologies can provide a more comprehensive and layered approach to payment data security, offering businesses and customers enhanced protection against fraud and unauthorized access.
Future Trends in Credit Card Tokenization
Credit card tokenization has already transformed the payment security landscape, but the technology continues to evolve and adapt to changing industry needs. Here are some future trends in credit card tokenization:
Biometric Tokenization: The integration of biometric authentication with tokenization is an emerging trend. By combining biometric factors such as fingerprints or facial recognition with tokenized payment data, businesses can further enhance security and streamline the user experience. Biometric tokenization adds an additional layer of authentication and prevents unauthorized access even if the token is compromised.
Tokenization for New Payment Methods: As new payment methods and technologies emerge, such as mobile wallets and wearables, tokenization will expand beyond traditional credit card transactions. Tokenization systems will need to support these new payment methods, ensuring secure and seamless transactions across a growing range of platforms.
Blockchain and Distributed Ledger Technology: Blockchain and distributed ledger technology (DLT) have the potential to revolutionize tokenization. By leveraging the decentralized nature of blockchain, tokenization can enhance security by eliminating single points of failure and providing immutable transaction records. Blockchain-based tokenization can also enable seamless cross-border transactions and facilitate interoperability between different payment systems.
Universal Tokenization Standards: Currently, tokenization standards can vary among different payment service providers and platforms, making interoperability a challenge. However, there is a growing push for universal tokenization standards to ensure compatibility and ease of integration. Efforts by industry consortiums and organizations, such as EMVCo, aim to establish common tokenization frameworks, making it easier for businesses to implement and manage token-based payment systems.
Integration with Artificial Intelligence (AI) and Machine Learning (ML): The integration of AI and ML technologies with tokenization can further enhance payment security. AI and ML algorithms can analyze customer behavior, transaction patterns, and other data points to detect anomalies and identify potential fraudulent activities. By combining these analytics capabilities with tokenization, businesses can proactively identify and mitigate security threats.
Tokenization beyond Card Data: While tokenization is primarily used for securing credit card data, its applications can extend beyond payment transactions. Tokenization can be used to protect other sensitive data, such as personal identification numbers (PINs), social security numbers, and bank account information. Tokenization can provide a comprehensive data protection strategy, offering businesses a unified approach to securing various types of sensitive information.
Enhanced Mobile Security: With the increasing use of mobile devices for payment transactions, tokenization will play a crucial role in securing mobile payments. Tokenization can safeguard mobile payment apps and protect the sensitive payment data stored on smartphones. As mobile payments continue to grow, advancements in mobile tokenization will be key to ensuring safe and convenient transactions.
These future trends in credit card tokenization reflect the ongoing need for secure payment solutions in an ever-evolving digital landscape. From biometric authentication to blockchain integration, businesses and payment service providers will continue to innovate and adapt tokenization to address emerging challenges and deliver enhanced payment security.
Conclusion
Credit card tokenization is a powerful technology that revolutionizes payment security by replacing sensitive card information with unique tokens. It offers numerous benefits, including enhanced security, simplified compliance, faster payment processing, increased customer trust, and a seamless user experience. By implementing credit card tokenization, businesses can protect their customers’ financial data, reduce the risk of fraud and data breaches, and create a secure payment environment.
While credit card tokenization is highly effective in securing payment transactions, it is important to consider the challenges and implementation considerations. Businesses need to navigate complexities such as integration with existing systems, compliance with industry regulations, and selecting a reputable tokenization solution provider. By addressing these challenges and ensuring proper training and awareness among employees, businesses can successfully implement credit card tokenization.
Looking towards the future, credit card tokenization is poised to evolve and incorporate emerging technologies such as biometric authentication, blockchain, AI and ML, and expanding to protect other types of sensitive data. The industry is also working towards establishing universal tokenization standards to ensure seamless interoperability across different payment systems and platforms.
In conclusion, credit card tokenization offers a secure, efficient, and convenient method for safeguarding payment data. By adopting this technology and staying informed about the evolving landscape, businesses can stay ahead of security threats, build customer trust, and provide a seamless payment experience in the digital age.